RSA 加密解密多语言实现方案
生成相关文件
- 生成模长为1024bit的私钥文件private_key.pem
cd rsa_multi_language
openssl genrsa -out private_key.pem 1024
- 生成IOS证书
1. 生成证书请求文件rsaCertReq-IOS.csr
openssl req -new -key private_key.pem -out rsaCerReq-IOS.csr
2. 生成证书rsaCert.crt,并设置有效时间为10年
openssl x509 -req -days 36500 -in rsaCerReq-IOS.csr -signkey private_key.pem -out rsaCert-IOS.crt
3. 生成供iOS使用的公钥文件public_key.der
openssl x509 -outform der -in rsaCert-IOS.crt -out public_key-IOS.der
4. 生成供iOS使用的私钥文件private_key.p12
openssl pkcs12 -export -out private_key-IOS.p12 -inkey private_key.pem -in rsaCert-IOS.crt
密码:sirenbang

- 生成供Java使用的私钥pkcs8_private_key.pem
openssl pkcs8 -topk8 -in private_key.pem -out pkcs8_private_key.pem -nocrypt
- 生成通用公钥rsa_public_key.pem
openssl rsa -in private_key.pem -out rsa_public_key.pem -pubout
- 生成rsa公钥 供python等使用 py_public_key.pem
openssl rsa -in private_key.pem -RSAPublicKey_out -out py_public_key.pem
代码
JAVA代码
工具类:
import org.bouncycastle.asn1.ASN1Sequence;
import org.bouncycastle.asn1.pkcs.RSAPrivateKeyStructure;
import org.bouncycastle.jce.provider.BouncyCastleProvider;
import sun.misc.BASE64Decoder;
import javax.crypto.Cipher;
import java.io.BufferedReader;
import java.io.InputStream;
import java.io.InputStreamReader;
import java.security.Key;
import java.security.KeyFactory;
import java.security.interfaces.RSAPrivateKey;
import java.security.interfaces.RSAPublicKey;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.RSAPrivateKeySpec;
import java.security.spec.X509EncodedKeySpec;
public class RSAEncryptUtils {
public static RSAPublicKey loadPublicKey(InputStream in) {
return loadPublicKey(readKeyAsString(in));
}
public static RSAPublicKey loadPublicKey(String publicKeyStr) {
try {
BASE64Decoder base64Decoder = new BASE64Decoder();
byte[] buffer = base64Decoder.decodeBuffer(publicKeyStr);
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
X509EncodedKeySpec keySpec = new X509EncodedKeySpec(buffer);
return (RSAPublicKey) keyFactory.generatePublic(keySpec);
} catch (Exception e) {
throw new RuntimeException(e);
}
}
public static RSAPrivateKey loadPrivateKey(InputStream in) {
return loadPrivateKey(readKeyAsString(in));
}
public static RSAPrivateKey loadPrivateKey(String privateKeyStr) {
//pkcs8
try {
BASE64Decoder base64Decoder = new BASE64Decoder();
byte[] buffer = base64Decoder.decodeBuffer(privateKeyStr);
PKCS8EncodedKeySpec keySpec = new PKCS8EncodedKeySpec(buffer);
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
return (RSAPrivateKey) keyFactory.generatePrivate(keySpec);
} catch (Exception ex) {
//pkcs1
try {
RSAPrivateKeyStructure asn1PrivKey = new RSAPrivateKeyStructure((ASN1Sequence) ASN1Sequence.fromByteArray(new BASE64Decoder().decodeBuffer(privateKeyStr)));
RSAPrivateKeySpec rsaPrivKeySpec = new RSAPrivateKeySpec(asn1PrivKey.getModulus(), asn1PrivKey.getPrivateExponent());
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
return (RSAPrivateKey) keyFactory.generatePrivate(rsaPrivKeySpec);
} catch (Exception e) {
throw new RuntimeException(e);
}
}
}
public static byte[] encrypt(Key publicOrPrivateKey, byte[] data) {
return endecrypt(publicOrPrivateKey, data, Cipher.ENCRYPT_MODE);
}
public static byte[] decrypt(Key publicOrPrivateKey, byte[] data) {
return endecrypt(publicOrPrivateKey, data, Cipher.DECRYPT_MODE);
}
private static byte[] endecrypt(Key publicOrPrivateKey, byte[] data, int mode) {
if (publicOrPrivateKey == null) {
throw new RuntimeException("加密或公钥不能为空");
}
Cipher cipher = null;
try {
cipher = Cipher.getInstance("RSA/ECB/PKCS1Padding", new BouncyCastleProvider());
cipher.init(mode, publicOrPrivateKey);
byte[] output = cipher.doFinal(data);
return output;
} catch (Exception e) {
throw new RuntimeException(e);
}
}
private static String readKeyAsString(InputStream in) {
try {
BufferedReader br = new BufferedReader(new InputStreamReader(in));
String readLine = null;
StringBuilder sb = new StringBuilder();
while ((readLine = br.readLine()) != null) {
if (readLine.charAt(0) == '-') {
continue;
} else {
sb.append(readLine);
sb.append('\r');
}
}
return sb.toString();
} catch (Exception e) {
throw new RuntimeException(e);
}
}
}
测试类:
import sun.misc.BASE64Decoder;
import sun.misc.BASE64Encoder;
import java.security.interfaces.RSAPrivateKey;
import java.security.interfaces.RSAPublicKey;
public class RSAEncryptTest {
public static void main(String[] args) {
RSAPublicKey rsaPublicKey = RSAEncryptUtils.loadPublicKey(RSAEncryptUtils.class.getResourceAsStream("/rsa_public_key.pem"));
RSAPrivateKey rsaPrivateKey = RSAEncryptUtils.loadPrivateKey(RSAEncryptUtils.class.getResourceAsStream("/pkcs8_private_key.pem"));
//测试字符串
String encryptStr = "aabbcc123我的";
System.out.println("原始字符串:" + encryptStr + "\n\n");
try {
//加密
byte[] cipher = RSAEncryptUtils.encrypt(rsaPublicKey, encryptStr.getBytes());
String encode = new BASE64Encoder().encode(cipher);
System.out.println("公钥加密后:" + encode);
cipher = (new BASE64Decoder().decodeBuffer(encode));
//解密
byte[] plainText = RSAEncryptUtils.decrypt(rsaPrivateKey, cipher);
System.out.println("私钥解密后:" + new String(plainText));
} catch (Exception e) {
System.err.println(e.getMessage());
}
System.out.println("\n\n");
try {
//加密
byte[] cipher = RSAEncryptUtils.encrypt(rsaPrivateKey, encryptStr.getBytes());
String encode = new BASE64Encoder().encode(cipher);
System.out.println("私钥加密后:" + encode);
cipher = (new BASE64Decoder().decodeBuffer(encode));
//解密
byte[] plainText = RSAEncryptUtils.decrypt(rsaPublicKey, cipher);
System.out.println("公钥解密后:" + new String(plainText));
} catch (Exception e) {
System.err.println(e.getMessage());
}
}
}
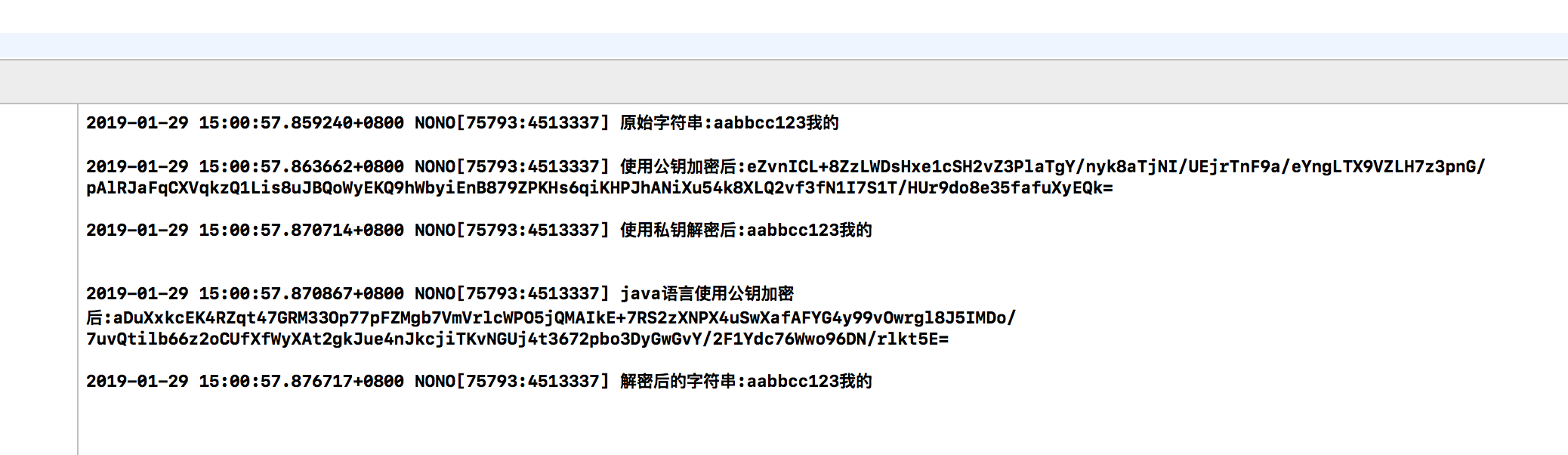
java代码运行结果:

IOS代码
RSAEncryptor.h :
#import <Foundation/Foundation.h>
@interface RSAEncryptor : NSObject
/**
* 加密方法
*
* @param str 需要加密的字符串
* @param path '.der'格式的公钥文件路径
*/
+ (NSString *)encryptString:(NSString *)str publicKeyWithContentsOfFile:(NSString *)path;
/**
* 解密方法
*
* @param str 需要解密的字符串
* @param path '.p12'格式的私钥文件路径
* @param password 私钥文件密码
*/
+ (NSString *)decryptString:(NSString *)str privateKeyWithContentsOfFile:(NSString *)path password:(NSString *)password;
/**
* 加密方法
*
* @param str 需要加密的字符串
* @param pubKey 公钥字符串
*/
+ (NSString *)encryptString:(NSString *)str publicKey:(NSString *)pubKey;
/**
* 解密方法
*
* @param str 需要解密的字符串
* @param privKey 私钥字符串
*/
+ (NSString *)decryptString:(NSString *)str privateKey:(NSString *)privKey;
@end
RSAEncryptor.m :
#import "RSAEncryptor.h"
#import <Security/Security.h>
static NSString *base64_encode_data(NSData *data){
data = [data base64EncodedDataWithOptions:0];
NSString *ret = [[NSString alloc] initWithData:data encoding:NSUTF8StringEncoding];
return ret;
}
static NSData *base64_decode(NSString *str){
NSData *data = [[NSData alloc] initWithBase64EncodedString:str options:NSDataBase64DecodingIgnoreUnknownCharacters];
return data;
}
@implementation RSAEncryptor
//加密
+ (NSString *)encryptString:(NSString *)str publicKeyWithContentsOfFile:(NSString *)path{
if (!str || !path) return nil;
return [self encryptString:str publicKeyRef:[self getPublicKeyRefWithContentsOfFile:path]];
}
//获取公钥
+ (SecKeyRef)getPublicKeyRefWithContentsOfFile:(NSString *)filePath{
NSData *certData = [NSData dataWithContentsOfFile:filePath];
if (!certData) {
return nil;
}
SecCertificateRef cert = SecCertificateCreateWithData(NULL, (CFDataRef)certData);
SecKeyRef key = NULL;
SecTrustRef trust = NULL;
SecPolicyRef policy = NULL;
if (cert != NULL) {
policy = SecPolicyCreateBasicX509();
if (policy) {
if (SecTrustCreateWithCertificates((CFTypeRef)cert, policy, &trust) == noErr) {
SecTrustResultType result;
if (SecTrustEvaluate(trust, &result) == noErr) {
key = SecTrustCopyPublicKey(trust);
}
}
}
}
if (policy) CFRelease(policy);
if (trust) CFRelease(trust);
if (cert) CFRelease(cert);
return key;
}
+ (NSString *)encryptString:(NSString *)str publicKeyRef:(SecKeyRef)publicKeyRef{
if(![str dataUsingEncoding:NSUTF8StringEncoding]){
return nil;
}
if(!publicKeyRef){
return nil;
}
NSData *data = [self encryptData:[str dataUsingEncoding:NSUTF8StringEncoding] withKeyRef:publicKeyRef];
NSString *ret = base64_encode_data(data);
return ret;
}
#pragma mark - 使用'.12'私钥文件解密
//解密
+ (NSString *)decryptString:(NSString *)str privateKeyWithContentsOfFile:(NSString *)path password:(NSString *)password{
if (!str || !path) return nil;
if (!password) password = @"";
return [self decryptString:str privateKeyRef:[self getPrivateKeyRefWithContentsOfFile:path password:password]];
}
//获取私钥
+ (SecKeyRef)getPrivateKeyRefWithContentsOfFile:(NSString *)filePath password:(NSString*)password{
NSData *p12Data = [NSData dataWithContentsOfFile:filePath];
if (!p12Data) {
return nil;
}
SecKeyRef privateKeyRef = NULL;
NSMutableDictionary * options = [[NSMutableDictionary alloc] init];
[options setObject: password forKey:(__bridge id)kSecImportExportPassphrase];
CFArrayRef items = CFArrayCreate(NULL, 0, 0, NULL);
OSStatus securityError = SecPKCS12Import((__bridge CFDataRef) p12Data, (__bridge CFDictionaryRef)options, &items);
if (securityError == noErr && CFArrayGetCount(items) > 0) {
CFDictionaryRef identityDict = CFArrayGetValueAtIndex(items, 0);
SecIdentityRef identityApp = (SecIdentityRef)CFDictionaryGetValue(identityDict, kSecImportItemIdentity);
securityError = SecIdentityCopyPrivateKey(identityApp, &privateKeyRef);
if (securityError != noErr) {
privateKeyRef = NULL;
}
}
CFRelease(items);
return privateKeyRef;
}
+ (NSString *)decryptString:(NSString *)str privateKeyRef:(SecKeyRef)privKeyRef{
NSData *data = [[NSData alloc] initWithBase64EncodedString:str options:NSDataBase64DecodingIgnoreUnknownCharacters];
if (!privKeyRef) {
return nil;
}
data = [self decryptData:data withKeyRef:privKeyRef];
NSString *ret = [[NSString alloc] initWithData:data encoding:NSUTF8StringEncoding];
return ret;
}
#pragma mark - 使用公钥字符串加密
/* START: Encryption with RSA public key */
//使用公钥字符串加密
+ (NSString *)encryptString:(NSString *)str publicKey:(NSString *)pubKey{
NSData *data = [self encryptData:[str dataUsingEncoding:NSUTF8StringEncoding] publicKey:pubKey];
NSString *ret = base64_encode_data(data);
return ret;
}
+ (NSData *)encryptData:(NSData *)data publicKey:(NSString *)pubKey{
if(!data || !pubKey){
return nil;
}
SecKeyRef keyRef = [self addPublicKey:pubKey];
if(!keyRef){
return nil;
}
return [self encryptData:data withKeyRef:keyRef];
}
+ (SecKeyRef)addPublicKey:(NSString *)key{
NSRange spos = [key rangeOfString:@"-----BEGIN PUBLIC KEY-----"];
NSRange epos = [key rangeOfString:@"-----END PUBLIC KEY-----"];
if(spos.location != NSNotFound && epos.location != NSNotFound){
NSUInteger s = spos.location + spos.length;
NSUInteger e = epos.location;
NSRange range = NSMakeRange(s, e-s);
key = [key substringWithRange:range];
}
key = [key stringByReplacingOccurrencesOfString:@"\r" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\n" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\t" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@" " withString:@""];
// This will be base64 encoded, decode it.
NSData *data = base64_decode(key);
data = [self stripPublicKeyHeader:data];
if(!data){
return nil;
}
//a tag to read/write keychain storage
NSString *tag = @"RSAUtil_PubKey";
NSData *d_tag = [NSData dataWithBytes:[tag UTF8String] length:[tag length]];
// Delete any old lingering key with the same tag
NSMutableDictionary *publicKey = [[NSMutableDictionary alloc] init];
[publicKey setObject:(__bridge id) kSecClassKey forKey:(__bridge id)kSecClass];
[publicKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
[publicKey setObject:d_tag forKey:(__bridge id)kSecAttrApplicationTag];
SecItemDelete((__bridge CFDictionaryRef)publicKey);
// Add persistent version of the key to system keychain
[publicKey setObject:data forKey:(__bridge id)kSecValueData];
[publicKey setObject:(__bridge id) kSecAttrKeyClassPublic forKey:(__bridge id)
kSecAttrKeyClass];
[publicKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)
kSecReturnPersistentRef];
CFTypeRef persistKey = nil;
OSStatus status = SecItemAdd((__bridge CFDictionaryRef)publicKey, &persistKey);
if (persistKey != nil){
CFRelease(persistKey);
}
if ((status != noErr) && (status != errSecDuplicateItem)) {
return nil;
}
[publicKey removeObjectForKey:(__bridge id)kSecValueData];
[publicKey removeObjectForKey:(__bridge id)kSecReturnPersistentRef];
[publicKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)kSecReturnRef];
[publicKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
// Now fetch the SecKeyRef version of the key
SecKeyRef keyRef = nil;
status = SecItemCopyMatching((__bridge CFDictionaryRef)publicKey, (CFTypeRef *)&keyRef);
if(status != noErr){
return nil;
}
return keyRef;
}
+ (NSData *)stripPublicKeyHeader:(NSData *)d_key{
// Skip ASN.1 public key header
if (d_key == nil) return(nil);
unsigned long len = [d_key length];
if (!len) return(nil);
unsigned char *c_key = (unsigned char *)[d_key bytes];
unsigned int idx = 0;
if (c_key[idx++] != 0x30) return(nil);
if (c_key[idx] > 0x80) idx += c_key[idx] - 0x80 + 1;
else idx++;
// PKCS #1 rsaEncryption szOID_RSA_RSA
static unsigned char seqiod[] =
{ 0x30, 0x0d, 0x06, 0x09, 0x2a, 0x86, 0x48, 0x86, 0xf7, 0x0d, 0x01, 0x01,
0x01, 0x05, 0x00 };
if (memcmp(&c_key[idx], seqiod, 15)) return(nil);
idx += 15;
if (c_key[idx++] != 0x03) return(nil);
if (c_key[idx] > 0x80) idx += c_key[idx] - 0x80 + 1;
else idx++;
if (c_key[idx++] != '\0') return(nil);
// Now make a new NSData from this buffer
return ([NSData dataWithBytes:&c_key[idx] length:len - idx]);
}
+ (NSData *)encryptData:(NSData *)data withKeyRef:(SecKeyRef) keyRef{
const uint8_t *srcbuf = (const uint8_t *)[data bytes];
size_t srclen = (size_t)data.length;
size_t block_size = SecKeyGetBlockSize(keyRef) * sizeof(uint8_t);
void *outbuf = malloc(block_size);
size_t src_block_size = block_size - 11;
NSMutableData *ret = [[NSMutableData alloc] init];
for(int idx=0; idx<srclen; idx+=src_block_size){
//NSLog(@"%d/%d block_size: %d", idx, (int)srclen, (int)block_size);
size_t data_len = srclen - idx;
if(data_len > src_block_size){
data_len = src_block_size;
}
size_t outlen = block_size;
OSStatus status = noErr;
status = SecKeyEncrypt(keyRef,
kSecPaddingPKCS1,
srcbuf + idx,
data_len,
outbuf,
&outlen
);
if (status != 0) {
NSLog(@"SecKeyEncrypt fail. Error Code: %d", status);
ret = nil;
break;
}else{
[ret appendBytes:outbuf length:outlen];
}
}
free(outbuf);
CFRelease(keyRef);
return ret;
}
/* END: Encryption with RSA public key */
#pragma mark - 使用私钥字符串解密
/* START: Decryption with RSA private key */
//使用私钥字符串解密
+ (NSString *)decryptString:(NSString *)str privateKey:(NSString *)privKey{
if (!str) return nil;
NSData *data = [[NSData alloc] initWithBase64EncodedString:str options:NSDataBase64DecodingIgnoreUnknownCharacters];
data = [self decryptData:data privateKey:privKey];
NSString *ret = [[NSString alloc] initWithData:data encoding:NSUTF8StringEncoding];
return ret;
}
+ (NSData *)decryptData:(NSData *)data privateKey:(NSString *)privKey{
if(!data || !privKey){
return nil;
}
SecKeyRef keyRef = [self addPrivateKey:privKey];
if(!keyRef){
return nil;
}
return [self decryptData:data withKeyRef:keyRef];
}
+ (SecKeyRef)addPrivateKey:(NSString *)key{
NSRange spos = [key rangeOfString:@"-----BEGIN RSA PRIVATE KEY-----"];
NSRange epos = [key rangeOfString:@"-----END RSA PRIVATE KEY-----"];
if(spos.location != NSNotFound && epos.location != NSNotFound){
NSUInteger s = spos.location + spos.length;
NSUInteger e = epos.location;
NSRange range = NSMakeRange(s, e-s);
key = [key substringWithRange:range];
}
key = [key stringByReplacingOccurrencesOfString:@"\r" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\n" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\t" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@" " withString:@""];
// This will be base64 encoded, decode it.
NSData *data = base64_decode(key);
data = [self stripPrivateKeyHeader:data];
if(!data){
return nil;
}
//a tag to read/write keychain storage
NSString *tag = @"RSAUtil_PrivKey";
NSData *d_tag = [NSData dataWithBytes:[tag UTF8String] length:[tag length]];
// Delete any old lingering key with the same tag
NSMutableDictionary *privateKey = [[NSMutableDictionary alloc] init];
[privateKey setObject:(__bridge id) kSecClassKey forKey:(__bridge id)kSecClass];
[privateKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
[privateKey setObject:d_tag forKey:(__bridge id)kSecAttrApplicationTag];
SecItemDelete((__bridge CFDictionaryRef)privateKey);
// Add persistent version of the key to system keychain
[privateKey setObject:data forKey:(__bridge id)kSecValueData];
[privateKey setObject:(__bridge id) kSecAttrKeyClassPrivate forKey:(__bridge id)
kSecAttrKeyClass];
[privateKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)
kSecReturnPersistentRef];
CFTypeRef persistKey = nil;
OSStatus status = SecItemAdd((__bridge CFDictionaryRef)privateKey, &persistKey);
if (persistKey != nil){
CFRelease(persistKey);
}
if ((status != noErr) && (status != errSecDuplicateItem)) {
return nil;
}
[privateKey removeObjectForKey:(__bridge id)kSecValueData];
[privateKey removeObjectForKey:(__bridge id)kSecReturnPersistentRef];
[privateKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)kSecReturnRef];
[privateKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
// Now fetch the SecKeyRef version of the key
SecKeyRef keyRef = nil;
status = SecItemCopyMatching((__bridge CFDictionaryRef)privateKey, (CFTypeRef *)&keyRef);
if(status != noErr){
return nil;
}
return keyRef;
}
+ (NSData *)stripPrivateKeyHeader:(NSData *)d_key{
// Skip ASN.1 private key header
if (d_key == nil) return(nil);
unsigned long len = [d_key length];
if (!len) return(nil);
unsigned char *c_key = (unsigned char *)[d_key bytes];
unsigned int idx = 22; //magic byte at offset 22
if (0x04 != c_key[idx++]) return nil;
//calculate length of the key
unsigned int c_len = c_key[idx++];
int det = c_len & 0x80;
if (!det) {
c_len = c_len & 0x7f;
} else {
int byteCount = c_len & 0x7f;
if (byteCount + idx > len) {
//rsa length field longer than buffer
return nil;
}
unsigned int accum = 0;
unsigned char *ptr = &c_key[idx];
idx += byteCount;
while (byteCount) {
accum = (accum << 8) + *ptr;
ptr++;
byteCount--;
}
c_len = accum;
}
// Now make a new NSData from this buffer
return [d_key subdataWithRange:NSMakeRange(idx, c_len)];
}
+ (NSData *)decryptData:(NSData *)data withKeyRef:(SecKeyRef) keyRef{
const uint8_t *srcbuf = (const uint8_t *)[data bytes];
size_t srclen = (size_t)data.length;
size_t block_size = SecKeyGetBlockSize(keyRef) * sizeof(uint8_t);
UInt8 *outbuf = malloc(block_size);
size_t src_block_size = block_size;
NSMutableData *ret = [[NSMutableData alloc] init];
for(int idx=0; idx<srclen; idx+=src_block_size){
//NSLog(@"%d/%d block_size: %d", idx, (int)srclen, (int)block_size);
size_t data_len = srclen - idx;
if(data_len > src_block_size){
data_len = src_block_size;
}
size_t outlen = block_size;
OSStatus status = noErr;
status = SecKeyDecrypt(keyRef,
kSecPaddingNone,
srcbuf + idx,
data_len,
outbuf,
&outlen
);
if (status != 0) {
NSLog(@"SecKeyEncrypt fail. Error Code: %d", status);
ret = nil;
break;
}else{
//the actual decrypted data is in the middle, locate it!
int idxFirstZero = -1;
int idxNextZero = (int)outlen;
for ( int i = 0; i < outlen; i++ ) {
if ( outbuf[i] == 0 ) {
if ( idxFirstZero < 0 ) {
idxFirstZero = i;
} else {
idxNextZero = i;
break;
}
}
}
[ret appendBytes:&outbuf[idxFirstZero+1] length:idxNextZero-idxFirstZero-1];
}
}
free(outbuf);
CFRelease(keyRef);
return ret;
}
/* END: Decryption with RSA private key */
@end
测试代码(ViewController.m):
#import "ViewController.h"
#import "RSAEncryptor.h"
@interface ViewController ()
@end
@implementation ViewController
- (void)viewDidLoad {
[super viewDidLoad];
//原始字符串
NSString *originalString = @"aabbcc123我的";
NSString *public_key_path = [[NSBundle mainBundle] pathForResource:@"public_key-IOS.der" ofType:nil];
NSString *private_key_path = [[NSBundle mainBundle] pathForResource:@"private_key-IOS.p12" ofType:nil];
NSLog(@"原始字符串:%@\n", originalString);
//使用公钥加密
NSString *encryptStr = [RSAEncryptor encryptString:originalString publicKeyWithContentsOfFile:public_key_path];
NSLog(@"使用公钥加密后:%@\n", encryptStr);
//使用私钥解密
NSLog(@"使用私钥解密后:%@\n\n", [RSAEncryptor decryptString:encryptStr privateKeyWithContentsOfFile:private_key_path password:@"sirenbang"]);
//通过java代码使用公钥加密后的字符串
NSString * encryptedStrByJavaWithPublicKey = @"aDuXxkcEK4RZqt47GRM33Op77pFZMgb7VmVrlcWPO5jQMAIkE+7RS2zXNPX4uSwXafAFYG4y99vOwrgl8J5IMDo/7uvQtilb66z2oCUfXfWyXAt2gkJue4nJkcjiTKvNGUj4t3672pbo3DyGwGvY/2F1Ydc76Wwo96DN/rlkt5E=";
//解密java语言使用公钥加密后的字符串
NSLog(@"java语言使用公钥加密后:%@\n", encryptedStrByJavaWithPublicKey);
NSLog(@"解密后的字符串:%@", [RSAEncryptor decryptString:encryptedStrByJavaWithPublicKey privateKeyWithContentsOfFile:private_key_path password:@"sirenbang"]);
}
- (void)didReceiveMemoryWarning {
[super didReceiveMemoryWarning];
// Dispose of any resources that can be recreated.
}
@end
IOS代码运行结果:
Python代码
python代码没有验证过,但应该没啥问题
import rsa
import base64
# 导入key
with open('py_public_key.pem') as publickfile:
p = publickfile.read()
pubkey = rsa.PublicKey.load_pkcs1(p)
with open('private_key.pem') as privatefile:
p = privatefile.read()
privkey = rsa.PrivateKey.load_pkcs1(p)
bob_pub = pubkey
bob_priv = privkey
message = """{"id": "49187f817657ecd9d472562b16c0ec7c","ip": "180.168.161.194","user-agent": "iOS8.1 iPhone 5s","ts": "1478879016008","channel": "iOS"}"""
# 数据分割函数
def format_str(string, width):
format_list = [string[x:x+width] for x in range(0,len(string),width)]
return format_list
# 按大小分割数据
str_list = format_str(message,117)
# 加密
data_list = []
for _str in str_list:
data_list.append(base64.encodestring(rsa.encrypt(_str, bob_pub)))
# 解密
_data_list = []
for data in data_list.append:
_data_list.append(rsa.decrypt(base64.decodestring(data), bob_priv))
_message = "".join(_data_list.append)
print _message
- 随机毒鸡汤:丑人多作怪这句话不假,因为长得好看的,无理取闹叫撒娇。